
Hakkımızda
ABDSEC, özel sektör ve kamu kuruluşları için, en güncel koruma hizmeti sağlamaya yönelik zaafiyet araştırması ve istismar kodu (exploit) geliştirme gibi saldırı odaklı bilişim güvenliği hizmetleri sunan bir Ar&Ge firmadır.
Çekirdek kadromuzla, kamuya açık olarak paylaşılan zaafiyet bilgilerini incelemenin yanı sıra hedef sistemlerde zaafiyetin sömürülebilir durumda olduğunu ispatlayan (Proof-of-Concept) kodlar hazırlayarak siber güvenlik yeteneklerinizi arttırmanızı sağlıyoruz.
Yıllık danışmanlık hizmetimizden faydalanan müşterilerimize özel firma bünyesinde keşfettiğimiz zaafiyetler hakkında teknik bilgi ve hedef odaklı saldırıları engellemeye yönelik tavsiyeler sağlıyoruz.
Araştırma
Yaklaşık 20 yıldan beri, güvenlik araştırmacıları hedef sistemlerin saldırganlar tarafından elegeçirebilmesini sağlayabilecek farklı türlerde yazılım hatalarını keşfettiler.
Farklı teknikler kullanarak, fuzzing gibi, bahsi geçen zaafiyetler herhangi bir saldırıya maruz kalmadan keşfedilebilir. Her geçen gün artan siber saldırı imkanları gözönüne alındığında karşı önlemlerin alınması daha da önemli bir gereksinim olmaktadır.
Ev sahibi bütün pencereleri kapatmak zorunda olsa da hırsıza açık kalmış tek bir pencere yeter!
Geliştirme
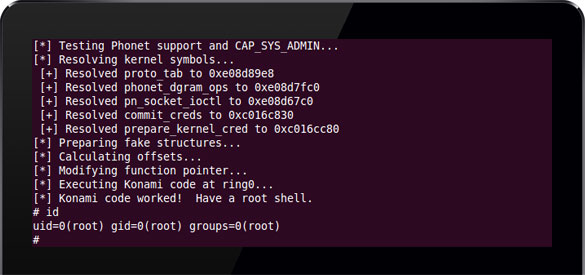
Defansa yönelik güvenlik yaklaşımı yüklenen programların ve alınan önlemlerin mümkün olan en yüksek korumayı sağlayacağı düşüncesini temel almaktadır. Malesef write-what-where (neyi-nereye-yaz) türünden bir zaafiyet alınan bütün önlemleri atlatmayı başarabilir.
Yeni bir zaafiyet keşfedildiğinde aşağıdaki sıralamayla beraber geliştirme süreci başlar:
- Zaafiyeti tetikleyen kod yolu belirlenir
- Sömürülebilirlik kontrol edilir
- İspat kodu (PoC) hazırlanır
- Engelleme yöntemleri atlatılır
- Exploit (istismar kodu) hazırlanır
Hizmetler
Kaynak Kod Analizi
Mevcut ya da yeni uygulamanızın kaynak kodunu yazılım hatalarına yönelik incelemeye tabi tutuyoruz. Satır satır incelemenin yanı sıra kaynak kodunuzu size overflow gibi güvenlik odaklı hazırlanmış derleyici eklentileri ile tekrar derleyerek özel testlerden geçiriyoruz.Uzmanlaştığımız diller; "C", "C++" ve "Java" dilleridir.
Örnek rapor için irtibata geçebilirsiniz
Tersine Mühendislik
Kaynak kodu bulunmayan uygulamaları, hedef mimarı ister "x86", "x86-64", "ARM" ya da "MIPS" olsun, tersine mühendislik yöntemleri ile inceliyoruz. GNU/GPL lisanslı açık kaynak programları kullanmanın yanı sıra başarı oranını yükseltebilmek adına ticari yazılımlar ile de incelemeler yapıyoruz.
Örnek rapor için irtibata geçebilirsinizSızma Testi
Alışılagelmiş sızma testleri Nessus, Metasploit ve Nmap scriptleri gibi ücretsiz ve ticari yazılımlar kullanılarak yapılır.
Hazır uygulamaları kullanarak yapılan testler, ANCAK hiç test yaptırmamaktan daha iyi sonuçlar vermektedir.
Gelişmiş Sızma Testi
Alışılagelmiş sızma testinin yanı sıra, bünyesinde Ar&Ge faaliyetleri bulunduran firmaların sundukları testlerde alınan başarı oranının yüksek olması bilinen bir gerçektir.
Sızma testi fiyatlandırması hedef sistemde kullanılan sunucu bilgisayalar + iş istasyonu + teste tabi tutulacak cihaz sayısı ve sosyal mühendislik testinin istenip istenmemesine bağlı olarak belirlenmektedir.
Detaylı fiyatlandırma için iletişime geçebilirsinizUygulamalı Eğitim
Uzmanlaştığımız konular ile alakalı şirket bünyemizde ya da müşterinin talep ettiği yerde uygulamalı eğitimler veriyoruz. Yurtdışı eğitimlerimiz, İngilizce olarak, sadece Körfez Arap ülkelerinde geçerlidir. Eğitim konularımız:
- Tersine Mühendislik Temelleri - x86
- Linux Uygulama Güvenliği - Exploit Geliştirme
- Linux Çekirdek (Kernel) Güvenliği - Exploit Geliştirme
Zararlı Yazılım Analizi
Linux temelli işletim sistemleri uygulamalarını (Android uygulamalar gibi) ve cihazları hedef alan zararlı yazılımları statik ve dinamik yöntemler kullanarak analiz ediyoruz.
Bir istismar kodu geliştirme sürecinde, varsayılan şifresi değiştirilmemiş ağ cihazlarını hedef alan, birçok anti-debugging tuzakları barındıran, zararlı yazılım hedef cihazları Dağıtık Devredışı Bırakma Saldırısı (DDoS) gerçekleştirebilmek için zombi haline getirmeyi hedefliyordu.
Örnek rapor için irtibata geçebilirsiniz

Kripto Paralar
Kriptoparaların popülerliği her geçen gün artarken, kullanılan algoritma ister SHA256D (Bitcoin) ya da Scrypt (Litecoin or Dogecoin) olsun, teknolojik altyapı ile alakalı kurumsal danışmanlık hizmetleri sunuyoruz:
- Teknik Altyapı [blockchain]
- Madenci Cihazların Kurulum ve İşletimi
- Madenci Cihazlar ve Cüzdan Güvenliği


